If we are to develop responsive theories that reflect and meet the urgent call for intervention that at times is a dull ache and at others is siren-loud, we have to start with our bodies, our lives, our experiences. What does surveillance look like? How do we recognize it?
The Racial Justice and Surveillance Network gathering at the Allied Media Conference brought together about 60 individuals and representatives from across the U.S. to continue conversation about the state of surveillance at large (e.g. data mining), as well as its racialized subsets (e.g. profiling).
When I joined with about seven participants in a small group break out session, we quickly decided it was important not to get lost in the weeds of broader theoretical perspectives of types of surveillance, but to focus on state surveillance, which was the reason we had come.
 Later, during another excellent small group activity, we used a root causes Tree of Knowledge* to flesh out what we meant by state surveillance. This prompted us to consider the causes, values, target/stakeholders, outcomes/solutions, and the external conditions of surveillance. It was a great activity that really got us talking about what we had come together for. The leave of the Tree of Knowledge or the specific ways that the issue manifests, but while this discussion touched upon specific experiences of surveillance, it largely remained in the realm of generalizations and abstractions.
Later, during another excellent small group activity, we used a root causes Tree of Knowledge* to flesh out what we meant by state surveillance. This prompted us to consider the causes, values, target/stakeholders, outcomes/solutions, and the external conditions of surveillance. It was a great activity that really got us talking about what we had come together for. The leave of the Tree of Knowledge or the specific ways that the issue manifests, but while this discussion touched upon specific experiences of surveillance, it largely remained in the realm of generalizations and abstractions.
When organizing it can be tempting and perhaps (emotionally) easier to swim (or float) into theoretical frameworks rather than wade through the challenges of our lived experiences. Abstractions are, by definition, generalizations and are therefore less visceral to discuss. Their use can provide a buffer from seemingly overwhelming and untenable truths. This space can provide much-needed emotional safety when taking on large scale, historic oppression such as racial injustice and surveillance.
But keeping distance from the specifics of personal experience necessarily means dissociating from the people who live that reality, potentially including our own selves. In addition, for people of privilege (in this case, those who are not acute targets of surveillance or racial injustice), use of abstractions can result in divisions between those who support a theory and those whose experience subverts the theory. At this gathering, it seems there were at least a few cases where this occurred in small groups.
A theory is a type of model. Models can be useful tools, especially when developed in a recursive check-and-balance relation with narratives of on the ground experiences. At the same time, because they are necessarily incomplete descriptions of what they represent, their omissions are to be expected but not forgotten, or else they can become stagnant liabilities.
Therefore, to be resilient, our theories of what surveillance is and how to address it must continually be informed by the stories of our lives. We don’t want to lose the big picture to the details, nor the specifics to the model.
There are many strategies to bring lived experience into the room, for example, the story circle process described by the People’s Organizing Committee. *** A word to the wise: during such story circles, I’ve found it important to remind everyone, but especially people with middle/upper class, or white, or academic privilege to keep telling a STORY, not to theorize about, or interpret the story. It’s amazing how hard it can be to simply tell what happened, but I’ve found that it’s from our experiences that we can leverage our collective genius.
 When we hear answers to these questions coming from individuals, we can not only develop more accurate theories, but also (as the Audre Lourde Project** describes it) “honor the experts” in the room: the people who have experience surveillance acutely and bodily (e.g. police searches), as well as the experts who have experienced it less invasively (e.g. online tracking.)
When we hear answers to these questions coming from individuals, we can not only develop more accurate theories, but also (as the Audre Lourde Project** describes it) “honor the experts” in the room: the people who have experience surveillance acutely and bodily (e.g. police searches), as well as the experts who have experienced it less invasively (e.g. online tracking.)
To that end, I propose that, before we discuss root causes, we tell stories and fill out another diagram to get on the same page of what we’re actually talking about. One version could be:
Tall Trees: What are the researched, peer-reviewed theories that describe what we’re talking about?
Low growing flowers and grasses: What are the “on the street” or “daily life” ways that people talk about this?
Ground: What are the specific, lived experiences that people have of this?
With a grounding in “what we are talking about,” conversations will include not only the topics but also the people talking. Our brilliant minds can then navigate these joint landscapes, keeping our theories accountable to our experiences, and our people connected to one another.
Footnotes:
* Root Causes Tree of Knowledge
Draw a tree. Then fill in the image with the following:
Roots: What are the root causes of surveillance?
Bark: What are the values and belief systems that allow for surveillance? What are the values and belief systems that guide our work/organizing?
Branches: Who are the targets and opposition on this issue? Who are key stakeholders that need to be mobilized?
Leaves: How is the problem manifesting itself today? (specific examples) What solutions are we fighting for?
Clouds: (optional) What external conditions should we consider that are affected by surveillance?
**Audre Lourde Project http://alp.org
***People’s Organizing Story Circle Model
http://www.peoplesorganizing.org/Volunteer/The%20Story%20Circle%20Model.doc
**** Theories are not only the domain of the academic. Be sure to include other resources such as those generated by citizen science groups.
Privacy & Surveillance Info & Links:
Center for Media Justice Panel: “InSecurity: Race, Surveillance and Privacy in the Digital Age”
https://www.youtube.com/watch?v=waw_zMsMfF8
Center for Media Justice Blog Post: Surveillance and Social Control: The Conversation We Need to be Having
Stop LAPD Spying Resources
http://stoplapdspying.org/resources/download/
Surveillance Self Defense
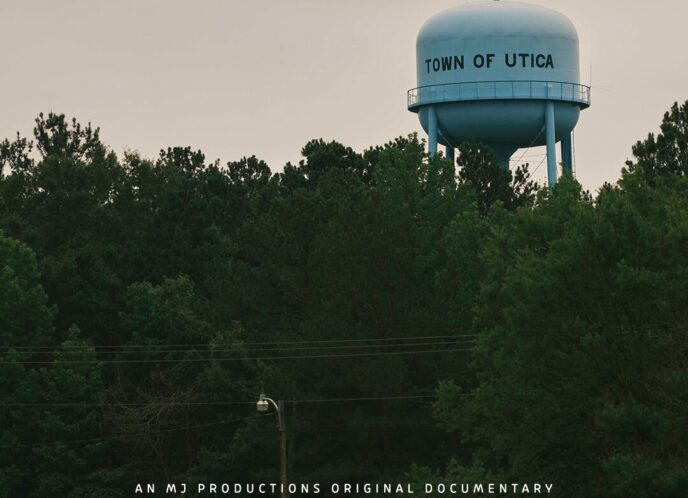
Tracked in America
http://www.trackedinamerica.org/
ALA’s Choose Privacy Week
Electronic Privacy Information Center
http://epic.org/privacy/surveillance/spotlight/
Articles:
I’ve Got Nothing to Hide (and other misunderstandings of privacy) http://papers.ssrn.com/sol3/papers.cfm?abstract_id=998565
Washington Post: Top Secret America
Short recap: http://stoplapdspying.org/top-secret-america-washington-post/
Interactive media with the in-depth article: http://projects.washingtonpost.com/top-secret-america/
Hayes, C. M., and Bashir, M. “Information Privacy and Data Control in Cloud Computing: Consumers, Privacy Preferences, and Market Efficiency.” Washington and Lee Law Review, Forthcoming, Illinois Program in Law, Behavior and Social Science Paper No. LBSS12-11, Illinois Public Law Research Paper No. 11-20. Jan 11, 2013.
Pfleeger, S., Rogers, M., Bashir, M., Caine, K., Caputo, D., Losavio, M. & Stolfo, S. Does profiling make us more secure? Privacy & Security: IEEE, 10 (4), 10-15, 2012.
Bashir, M., Kesan, J., Hayes, C., Zielinski; R., “Privacy in the cloud: Going beyond the contractarian paradigm.” In Proceedings of the 2011 Workshop on Governance of Technology, Information, and Policies (GTIP ’11), Dec. 2011 doi: 10.1145/2076496.2076499.